We all know that data breaches cost a lot—an average of $3.6 million per organization. For cyber criminals, everyone’s a target—and perfect prevention isn’t practical. We must assume that, at some point, every organization’s IT infrastructure will be breached.

That’s why as Managed Service Providers (MSPs), it is important to continuously monitor, investigate, and respond to cyber threats within your client’s systems 24/7/365. If you help your clients avoid costly breaches and the potential impact to their reputation, revenue, and customer confidence, you will build trust and loyalty with your client base.
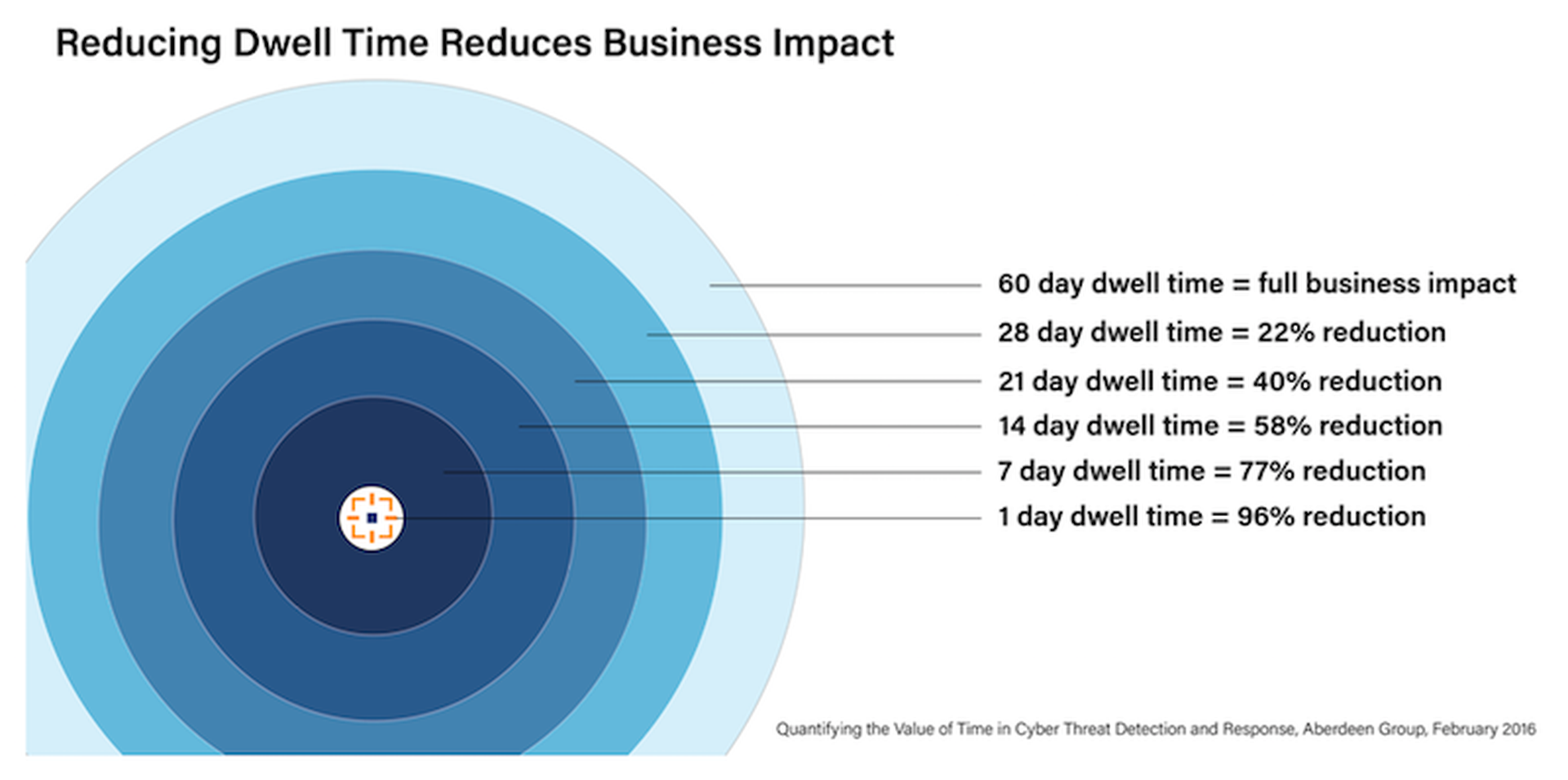
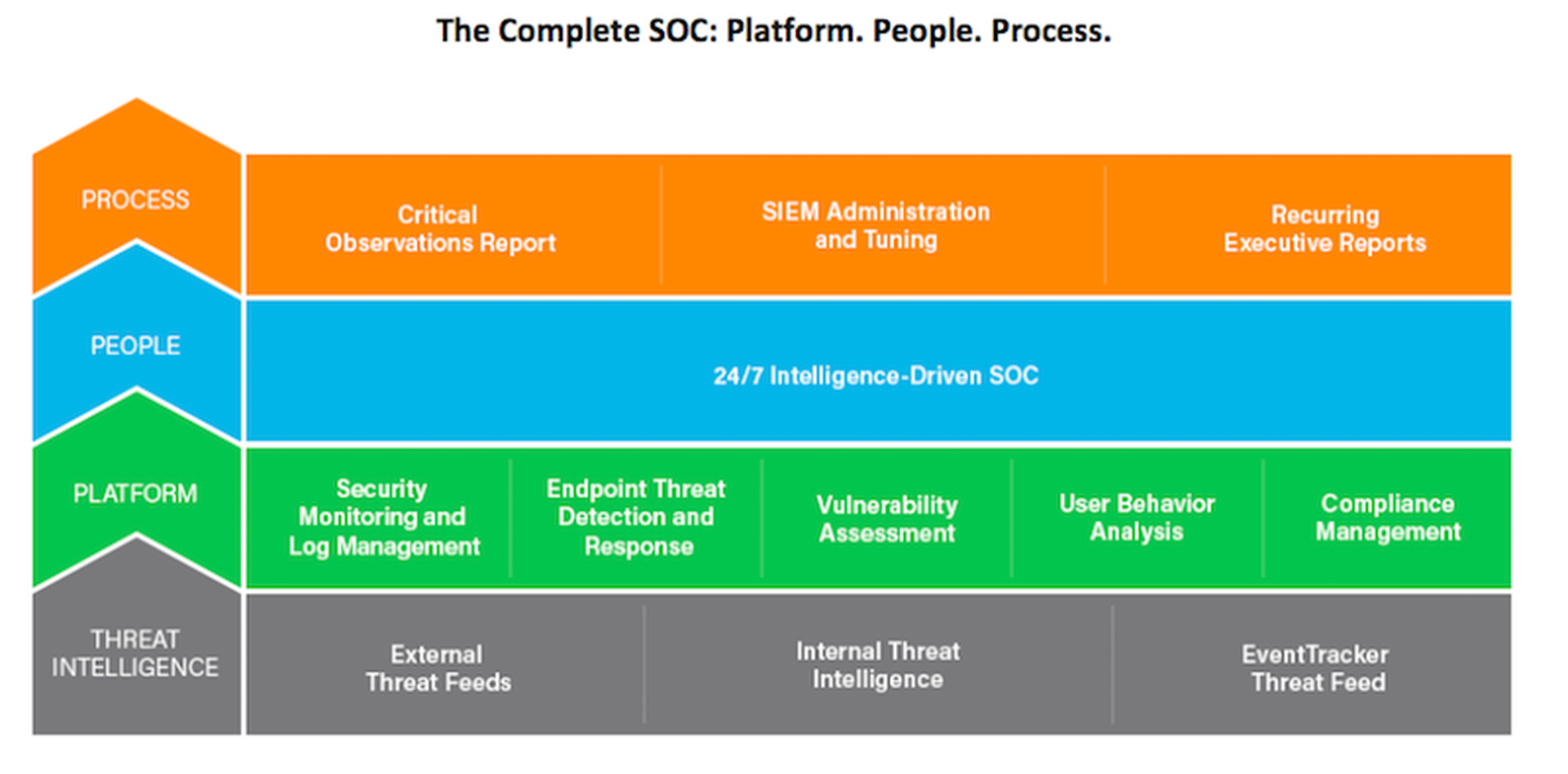
What better way to provide continuous monitoring and analysis than through a security operations center (SOC)? With the people, processes, and platform to continuously look across an entire organization’s networks, servers, endpoints, applications, and databases, a SOC applies expert knowledge to detect and dig into potential threats. One of the key benefits of a SOC is preventing the devastating impact of a breach by reducing the dwell time (the time between when an attacker compromises a network—minutes—and when the organization discovers the threat—typically months!)
Cost and complexity are roadblocks
Any way you look at it, a SOC is complex and expensive. It requires a lot of specialized hardware and software to generate events and alerts, which must be examined by highly skilled security analysts who can determine which ones represent real threats.
The platform is costly. You need a well-tuned SIEM (security information and event management) to provide the visibility foundation, along with firewalls, IPS/IDS, vulnerability assessment tools, endpoint monitoring solutions, and more. All of this must be fed by threat intelligence that is specific to your organization’s goals and risk tolerance, and the results need to be augmented by machine learning and fine-tuned by human experts.
Processes are costly as well. Detailed organization-specific playbooks need to be written, spelling out what should happen when ransomware, malware infections, distributed denial of service attacks, or other threats are seen. They specify how to investigate, what evidence to gather, and when and how to escalate.
Perhaps the most expensive component is people. It’s difficult to hire a team of highly skilled security analysts with the bandwidth and expertise to perform continuous monitoring, while we are experiencing a worldwide shortage of talent. It’s even harder to retain them in the face of stiff competition for these scarce resources.
The Complete SOC: Platform. People. Process.
Finding the best route
Reaching the goal of continuous coverage is not a simple make/buy decision: it’s more of a buy/rent/managed security service decision: should you build your own SOC, outsource your SIEM (or SOC) platform, or leverage a managed security service that includes a SOC.
- Building your own SOC is akin to buying a car to get from Point A to Point B. You incur all the platform, process, and people costs – but you are in total control over where you are going and how to get there (i.e. what your clients see as risks, threats, and responses). Of course, the cost and complexity could be prohibitive making your services costly for your clients. Taking this route could easily price smaller businesses out of choosing you as their MSP.
- Outsourcing your SIEM or SOC platform is like renting a car. You don’t have to make the capital outlay for hardware, but you still need to carry out all the processes—and you must hire, train, and retain your own SOC team. It’s less expensive than building your own SOC, but still quite pricey.
- Leveraging a managed security solution that includes a SOC is like using Uber to get to your destination. You augment your own internal team with seasoned security experts with mature processes driving a powerful SIEM platform, yet you remain in control of the ultimate destination. A managed SOC ensures that the collective team is operating in concert to reach your specific goals.
Uber your way to a SOC
The goal is to get from Point A (your client’s current security and compliance posture) to Point B (providing your clients a stronger security posture, compliance confidence, and incident readiness). Clearly, the most cost-effective way to reach that goal for the SMB market is via a managed security solution that includes a SOC – the Uber approach. You get the best of both worlds: the best people, processes, and platform, at the lowest cost. Not only do you avoid the people and process costs, you retain control over helping your clients improving their security posture. Maybe it’s time to follow the lead of the ride-sharing world, and take the smarter route to a SOC. EventTracker is the only managed security service provider that combines our own ISO-certified 24/7 SOC with our own award-winning SIEM platform for a truly integrated managed security service.
Guy Cunningham is VP of channel sales and alliances, EventTracker, a Netsurion company. Read more EventTracker blogs here. EventTracker is a Netsurion company.