As the world around us changes faster than ever, it’s not only reshaping human behavior but also our very identities.

This new paradigm shift focuses on designing products and services around both humans and non-humans (machines, bots, etc.). From a security standpoint the emerging challenge is managing and governing those identities effectively and securely.
Digital transformation (DX) represents a sea of opportunities to shape the future. One such prospect is the acceleration of cloud adoption, which has supercharged DX and allowed organizations to revamp their business models around improved interactions with consumers and employees. However, while most organizations have been on the DX journey for decades, they’ve only recently witnessed its acceleration, fueled primarily by the almost viral adoption of hybrid- or multi-cloud technology.
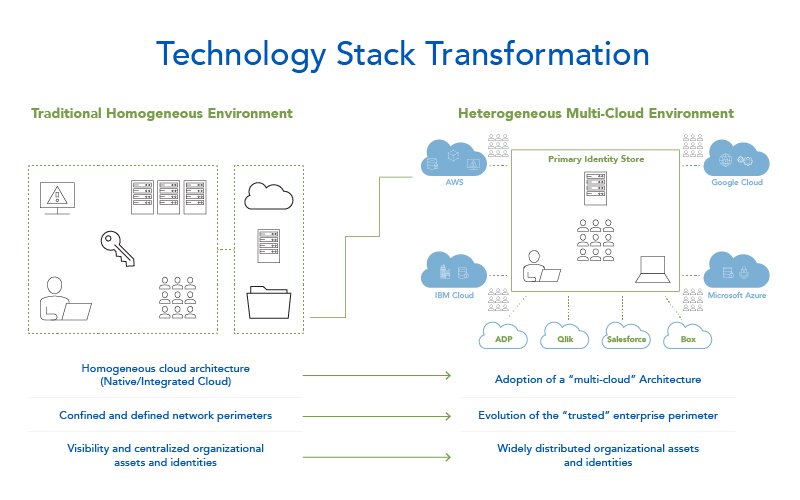
This blurred network perimeter and evolving workforce, further prove that assets and identities are no longer confined to traditional organizational boundaries. Unsurprisingly, managing assets and identities has become a daunting task with the potential to create inefficiencies and harm security and compliance.
Let’s look at a simplified view of the tech stack’s evolution after hybrid and multi-cloud adoption. The evolved ecosystem appears decentralized, uncontained and overall heterogeneous – factors that each complicate a tech stack’s security and operational posture.
So, the question becomes: how do you operate such an environment effectively and efficiently while maintaining your organization’s security and compliance posture?
Driving Towards an Identity-Centric Solution
As you look at this challenge holistically, an “identity-centric” approach is the most logical. The focus needs to be on safeguarding interactions between identities and cloud workloads by aligning the fundamentals of basic access controls.
Four key elements are required for an effective identity-centric solution:
- Visibility to identities that are accessing critical resources across workloads in a multi-cloud environment
- Strong enterprise-wide access controls, policies and guardrails across the hybrid, multi-cloud infrastructure
- Ongoing monitoring capabilities to detect, record and prevent abnormal access and configurations associated with critical resources
- Proactive decision-making through automation and predictive analytics
Emergence of Cloud Access Governance Capabilities
To design an effective identity solution around these four key elements, it’s critical that we also explore and understand existing cloud management capabilities like cloud infrastructure entitlement management, or CIEM.
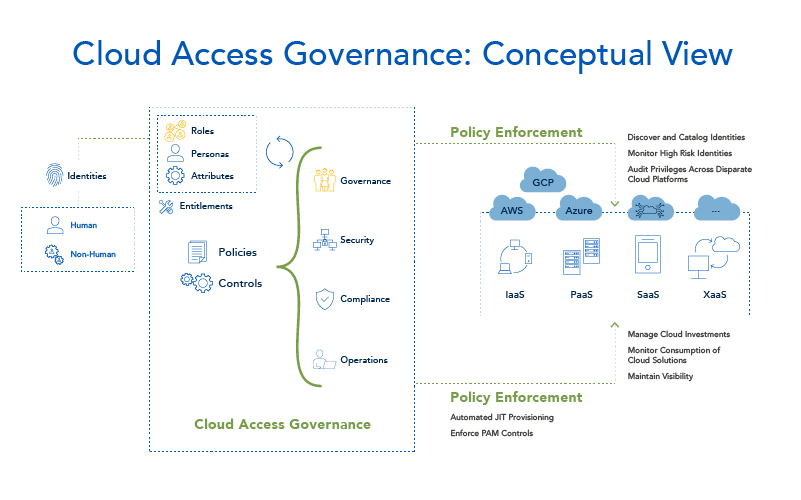
Our vision takes CIEM a step further. Rather than focusing on management of access over a specific cloud deployment model, cloud access governance (CAG) aims to extend the governance layer across all existing models.
This conceptual view shows the ways human and non-human entities interact with a hybrid-cloud infrastructure, and how a CAG capability defines and enforces guardrails over these interactions. While AWS and Azure may provide similar features for governing heterogeneous, multi-cloud environments, CAG integrates seamlessly with traditional on-premises identity governance and administration (IGA) capabilities. Think of it as an encapsulated layer providing a single watchtower to monitor and manage interactions.
Crafting a solution is one win, but cybersecurity professionals know the real challenge lies in practical implementation. So we’re building use cases with our technology partners to mimic the real world; these fall primarily into three categories: security, compliance and operations. While the use cases around security and compliance spotlight core access controls (provisioning, de-provisioning, access certification, least privilege, etc.), those within the operations category focus on, you guessed it, the operational elements (just-in-time provisioning, PAM, etc.).
Overlaying Zero Trust Core Principles
We mentioned earlier that the business and technology ecosystem is rapidly evolving thanks to factors like blurring network perimeters, a pervasive remote workforce and a distributed resource model. It shouldn’t be a surprise, then, that Zero Trust security is central to that discussion. As we apply these concepts in the real world, however, “identity-centric” security remains our north star.
It’s no secret that a Zero Trust model requires various core security capabilities to work in harmony. Although no one capability can satisfy the model alone, cloud access governance has potential to play a big role in the Zero Trust (like that of the policy decision point ). By combining appropriately defined guardrails and policies with active monitoring, CAG can keep a pulse on all entities interacting with resources as it continuously verifies their legitimacy and fulfills the role of a PDP in the Zero Trust model. Put simply, an effective cloud access governance design can align with Zero Trust principles and truly live by its mantra: never trust, always verify.
Conclusion
In the face of unprecedented digital disruption, security and risk management is quickly becoming one with core business strategies. Disruptions will bring challenges, but they’ll also shape the way we solve problems, setting the stage for a more effective, efficient and secure future. The key is to build solutions around the fundamental elements, which are essential to solving a security challenge.
In the world of security, one such fundamental element is identity. Although the very concept continues to evolve, identity will always be at the core of interactions with resources critical to businesses. A capability like cloud access governance enhances visibility, control and governance over these identities, offering a holistic solution to the emerging security challenges of a hybrid world.
Author Sagnik Mukherjee is senior practice manager at Optiv, a Top 250 MSSP.