Cyber adversaries will stop at nothing to carry out damaging attacks. With the right tools and resources at their disposal, attackers are becoming stealthier than ever at infiltrating networks, evading detection and moving laterally. And once they gain a foothold, they can utilize ‘living off the land’ techniques to mimic legitimate administrative behavior – all of which requires human eyes and a trained threat-hunting response team who know how to confirm malicious behavior and neutralize threats.
A comprehensive, defense-in-depth cybersecurity strategy that emphasizes multiple layers of protection is absolutely critical for proactively defending against these stealthy attacks. Endpoint detection and response (EDR) is one essential tool for doing this; a set of trained human eyes is another.
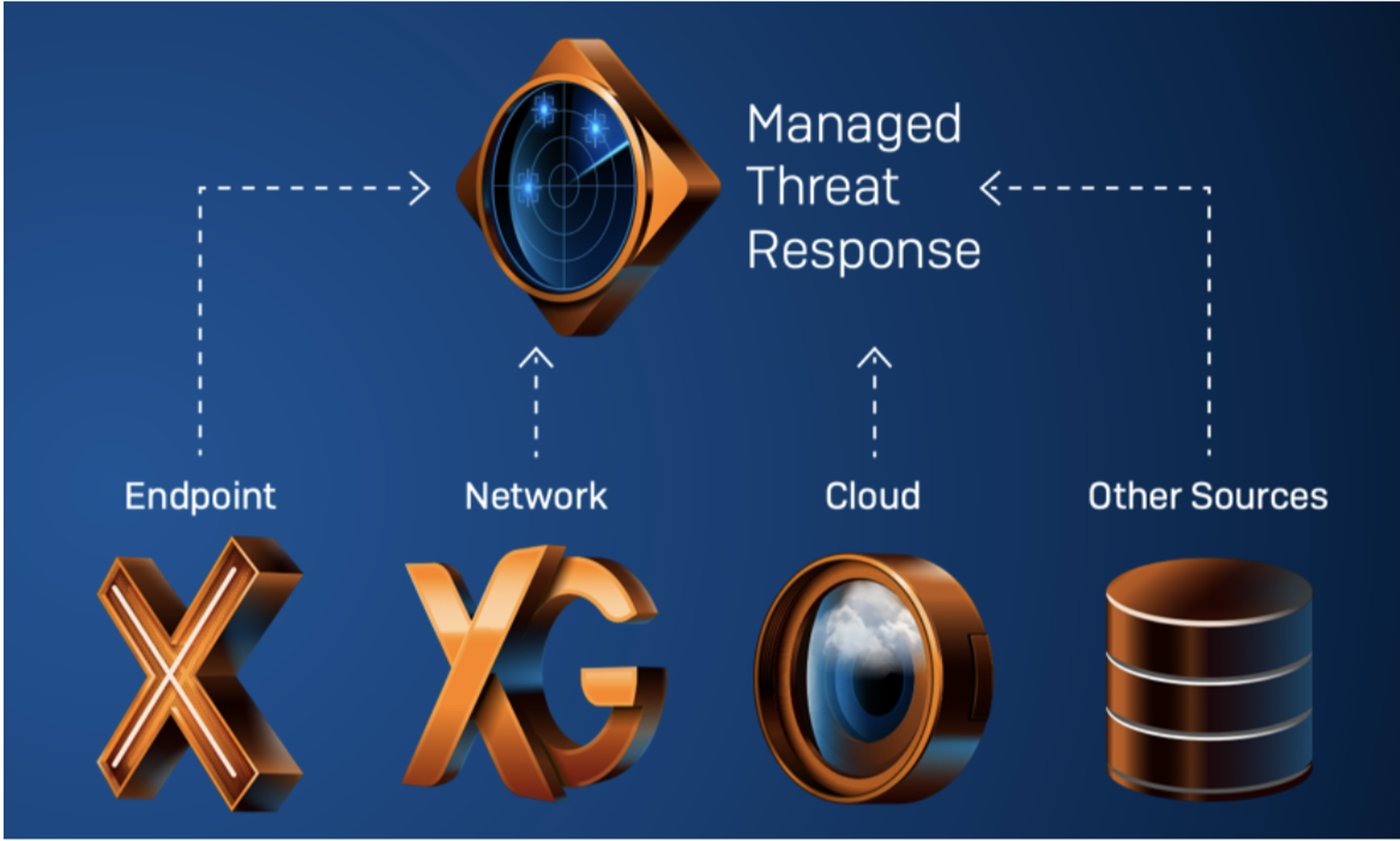
Sophos Managed Threat Response (MTR) provides the best of both worlds, fusing the machine learning of EDR with expert human analysis, for an evolved approach to proactive security protection. Organizations benefit with Sophos’ consistently top-rated endpoint protection and intelligent EDR, combined with a world-class team of security experts in what we call “machine-accelerated human response.”
This expert team works 24/7 to identify and neutralize threats, provide security health checks to keep all of your Sophos Central products operating at peak performance and give you enhanced telemetry that extends beyond the endpoint to provide a full picture of adversary activities.
“Clients with successful SOCs put the premium on people rather than process and technology. People and process overshadow technology as predictors for SOC success or failure.”
Why Evolving Threats Highlight the Need to Outsource the SOC
The scope and scale of cyber threats facing organizations has grown dramatically. Ransomware, malware, potentially unwanted applications – these aren’t just the lingo of in-the-weeds IT workers; they’re serious risks on the minds of every major business leader. And it’s not just the volume of threats that’s the problem, but the sophistication of them. Some exploits now are so well-hidden and timed that they can circumvent even the most robust endpoint and network protection capabilities.
Sophos Managed Threat Response stands apart from those other capabilities, though. Competing services create more work for customers by simply providing just threat notifications, and then stopping there. But threat notification isn’t a solution, it’s just the starting point. At the same time, not all managed service providers (MSPs) have the right tools, people and processes in-house to effectively manage their security operations centers (SOCs) around the clock and proactively defend against new, emerging threats.
All the more reason to outsource your SOC to a third party that has the space and the resources to do both. Going beyond simply notifying you of attacks or suspicious behaviors, Sophos MTR goes the extra mile to take the targeted actions necessary to neutralize even the most sophisticated, complex and active threats, with the speed and precision they require.
When Rubber Meets the Road
The words “breach” and “incident response” are not words that an MSP typically likes to hear, but studies continue to show us that SMBs are the most attacked and subsequently the most vulnerable to these threats.
As the responsibilities of maintaining cyber resiliency for your clients grows, so does the need to be as prepared as possible for an attack. Too often do we see SMB victims of cyberattacks seek reparation from the guardians that they trusted the security of their business with – i.e., the MSP. But hackers are using tactics that quite simply can catch MSPs off guard. In the event of a breach, you need to be able to get in touch immediately with expert threat analysts who can support you with more than just an email alert.
Sophos MTR delivers this rapid response capability, offering you incident response and 24/7 monitoring with an expert team of real human threat analysts, who are trained to quickly take action to triage, contain and neutralize active threats within your or your clients’ environment. Sophos MTR also proactively improves your security posture and hardens your defenses with prescriptive guidance for addressing configuration and architecture weaknesses that can otherwise diminish your overall security capabilities.
Activity Reporting
Sophos MTR analysts constantly review alerts, investigate anomalous activity and respond to confirmed threats with speed and precision based upon your selected preferences (i.e. response mode). In addition to providing comprehensive assessments of attacker activity and corresponding response actions as they occur, analysts also provide monthly activity reports summarizing case activities and providing the context needed to understand threats, assess organizational risk and prioritize actions.
Sophos MTR Service Tiers
Sophos MTR features two service tiers – standard and advanced – to provide a comprehensive set of capabilities for organizations of all sizes and maturity levels. Regardless of the service tier selected, organizations can take advantage of any of the three response modes (notify, collaborate or authorize) to fit their unique needs.
Sophos MTR: Standard
- 24/7 Lead-Driven Threat Hunting
Confirmed malicious artifacts or activity (strong signals) are automatically blocked or terminated, freeing up threat hunters to conduct lead-driven threat hunts. This type of threat hunt involves the aggregation and investigation of causal and adjacent events (weak signals) to discover new indicators of attack and compromise that previously could not be detected.
- Security Health Check
Keep your Sophos Central products – beginning with Intercept X Advanced with EDR – operating at peak performance with proactive examinations of your operating conditions and recommended configuration improvements.
- Activity Reporting
Summaries of case activities enable prioritization and communication so your team knows what threats were detected and what response actions were taken within each reporting period.
- Adversarial Detections
Most successful attacks rely on the execution of a process that can appear legitimate to monitoring tools. Using proprietary investigation techniques, our team determines the difference between legitimate behavior and the tactics, techniques and procedures (TTPs) used by attackers.
Sophos MTR: Advanced
Includes all standard features, plus the following:
- 24/7 Leadless Threat Hunting
Applying data science, threat intelligence and the intuition of veteran threat hunters, Sophos MTR anticipates attacker behaviors and identifies new indicators of attack and compromise.
- Enhanced Telemetry
Threat investigations are supplemented with telemetry from other Sophos Central products, extending beyond the endpoint to provide a full picture of adversary activities.
- Proactive Posture Improvement
Proactively improve your security posture and harden your defenses with prescriptive guidance for addressing configuration and architecture weaknesses that diminish your overall security capabilities.
The Sophos Next-Gen Advantage
Next-gen products and solutions are discussed frequently in the technology marketplace today. Sophos’ approach to next-gen architecture doubles down by combining the necessary elements of a layered security environment into an easy-to-navigate platform that gives you scalable levels of visibility and protection.
These combined layers of security within Sophos Central are also synchronized to share threat intelligence across products to stop threats in real time, making it one of the most effective and comprehensive cybersecurity systems available.
Adding Sophos MTR to the stack elevates your MSP security offering further, to where it can withstand attack and bring the reassurance of a trusted SOC to MSPs of any size.
Learn more about Sophos’ MTR services, or join Sophos’ award winning MSP Connect Flex program today.
Guest blog courtesy of at Sophos. Read more Sophos blogs here.




