To understand the role of Open XDR in implementing zero trust architecture (ZTA) it is first important to understand what ZTA is and how it has evolved.
In today's threat landscape, cyberattacks are persistent, sophisticated, and often difficult to detect as they blur the lines between insider and outsider threats. The trend towards more open and cloud-based systems, as well as the shift to remote work, the adoption of IoT, etc. are all expanding the attack surface and challenging the traditional notion of perimeter security. Thus, the shift to the ZTA approach to cybersecurity has grown in popularity and necessity.
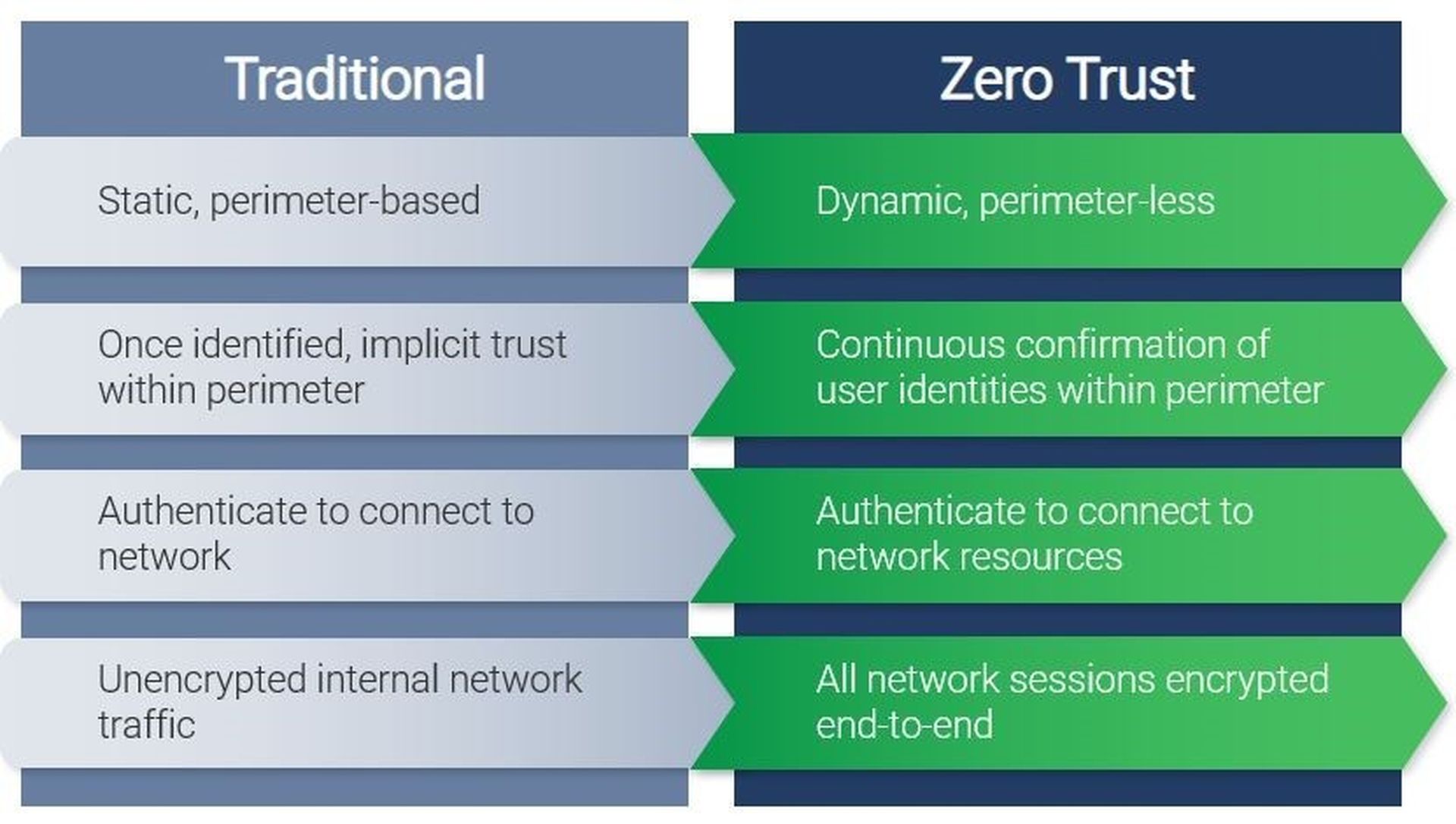
The Shift from Traditional to ZTA
The traditional architecture model assumed a well-defined perimeter, where once you were inside, you had free access to all resources within the network. This model was suitable for a simpler time when remote access was not as prevalent. Now ZTA has become the norm, where every interaction, regardless of whether it is a user or a device, inside or outside, if it wants to access a network resource it must be authenticated and authorized first.
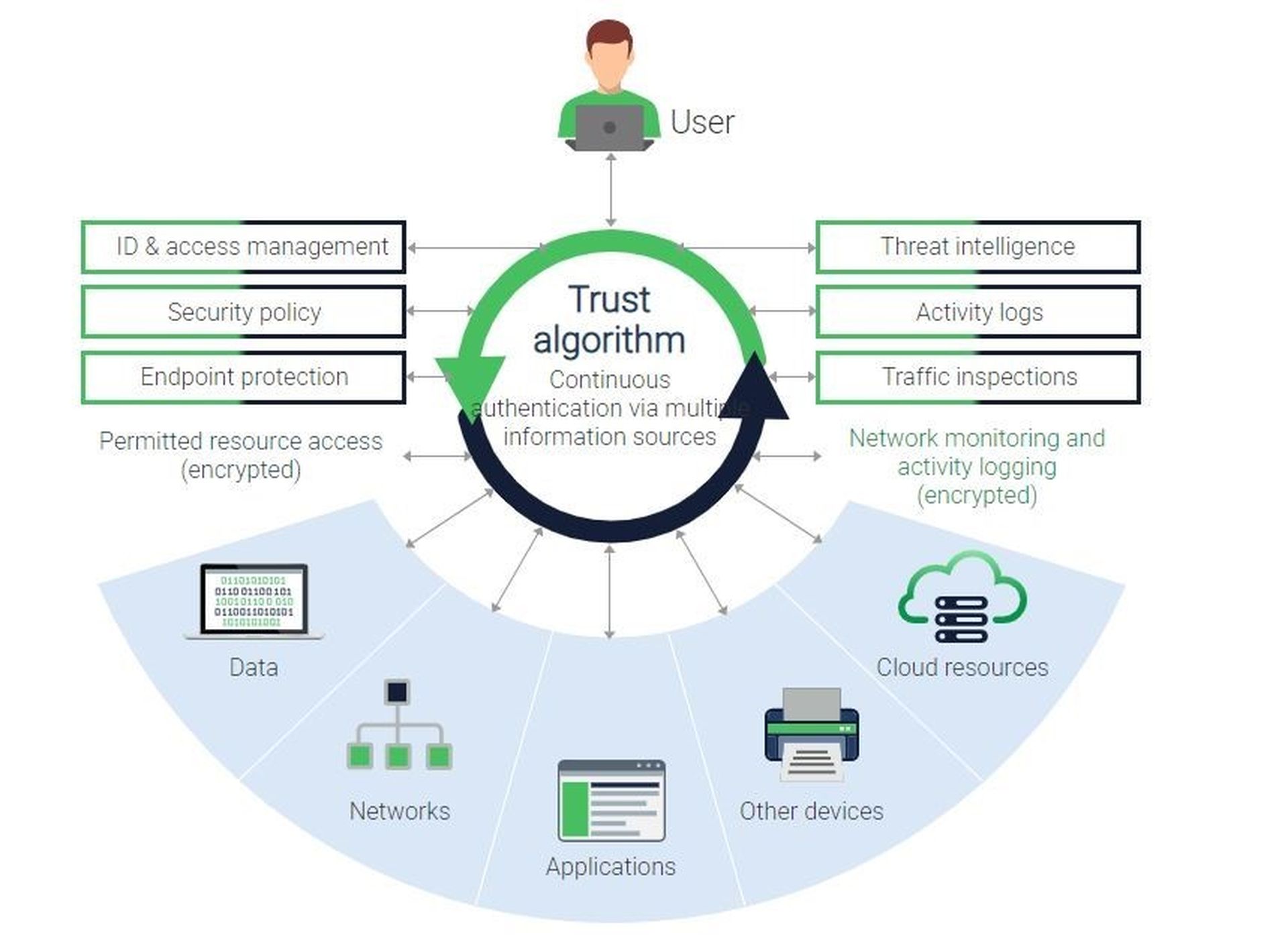
How does ZTA Work?
To implement ZTA, you need a security policy that defines which users and devices are granted or denied access to a resource. This policy is applied by a trust algorithm that grants or denies access to a resource based on the policy. In addition, you need an identity credential system, security analytics (threat intelligence, logs, UEBA), endpoint protection, and all traffic encrypted.
Roles of Open XDR in Implementing ZTA
How does Open XDR help with implementing ZTA? Open XDR solutions combine technologies including log collection, threat intelligence & detection, endpoint protection, and network traffic analysis.
The "Open" part of Open XDR means that you can keep any decisions regarding the technology you already have in place and allows centralized visibility across these data sources including credential systems, authentication mechanisms, endpoints, operating systems, VPNs, firewalls, and networks.
This provides a comprehensive integrated approach to security monitoring and threat detection and allows security teams to monitor all activity across an organization and detect potential threats in real-time.
Benefits of Implementing ZTA with Open XDR
- Confine security incidents. When an incident does occur limiting the blast radius is critical. With Zero Trust if a user or device is compromised, the potential damage is limited to only those resources to that which they have been granted access.
- Improve situational awareness. With continuous monitoring, you will have insights into what’s normal in your network which is important for detecting any suspicious activity or deviations from normal patterns. This allows security teams to respond quickly to potential threats.
- Enhance data confidentiality. Implementing a comprehensive and multi-layered security approach ensures that only authorized personnel can access sensitive data and that data remains protected from potential threats
- Scalability. As your business grows and evolves, the Open XDR solution can adapt to your changing technology choices without any demand to purchase specific products.
Brining it All Together
Implementing an Open XDR solution with the ZTA can provide a comprehensive approach to network security, enabling you to authenticate and authorize every interaction. This can help you limit the blast radius, improve situational awareness, enhance data confidentiality, and scale your network security as your business grows.
Check out Netsurion’s Managed XDR solution and Npower Partner Program for further insights on how we can help you implement ZTA with a scalable and flexible approach.
Author A.N. Ananth is Chief Strategy Officer for Netsurion. Read more Netsurion guest blogs here. Regularly contributed guest blogs are part of MSSP Alert’s sponsorship program.




