California lawmakers are tackling Internet of Things (IoT) security from the ground up with a new bill that mandates manufacturers affix unique passwords onto their connected devices.
For consumers, it’s obviously a good thing. For device makers, we’re talking about securing a lot of stuff, from networking gear to smart home gadgets. More stuff means more buyers means more revenue. No matter, IoT security regulation’s time has come and none too soon. A recent study by security provider Kaspersky found that 93 percent of malware attacks it counted in its labs came from brute force password assaults.
For cyber gangsters, it might make it a bit rockier to zombie-ize hundreds of thousands of devices into distributed denial of service (DDoS) armies. Nothing wrong with that -- remember the 2016 Mirai botnet that crippled websites worldwide?
And, for managed security service providers, it adds a layer endpoint security not heretofore available.
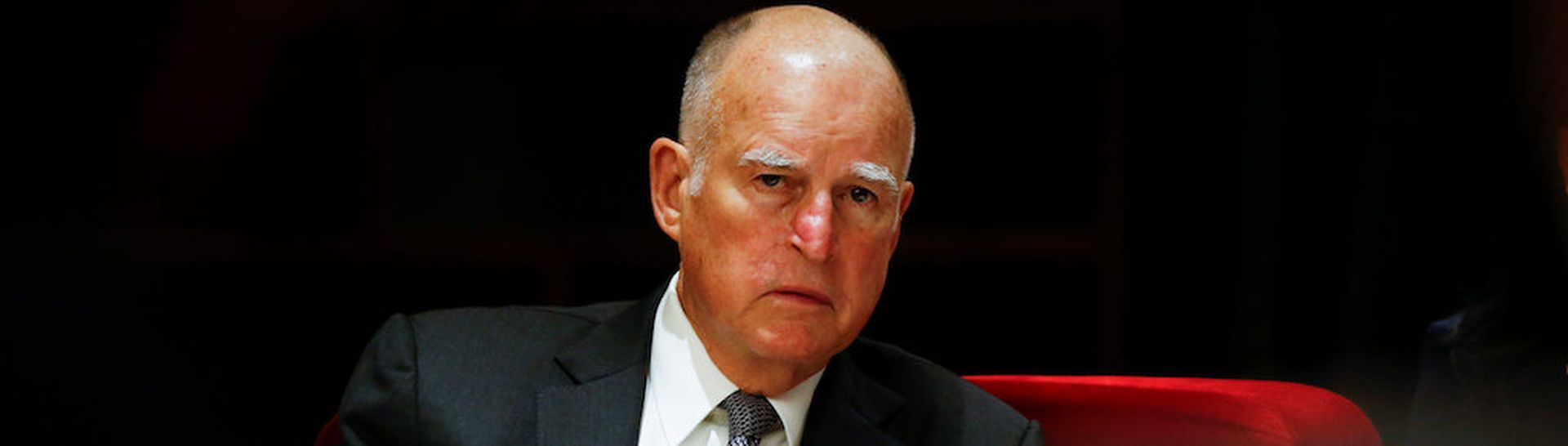
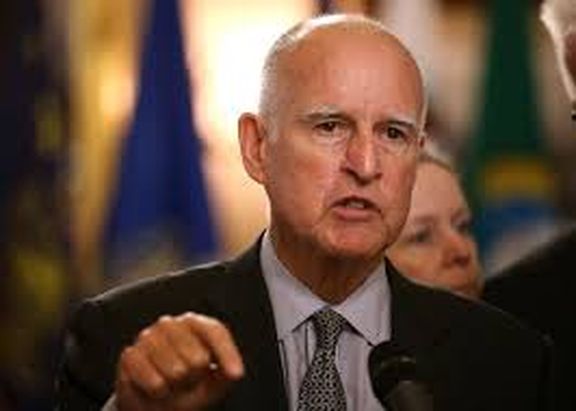
If Governor Jerry Brown signs Information privacy: connected devices (SB-327) it will be the first IoT device security regulation to come into effect in the U.S., beating the federal government to the punch by a wide margin.
Here are the law’s nuts and bolts:
- A manufacturer of a connected device must equip the device with a “reasonable security feature or features.”
- Appropriate to the nature and function of the device.
- Appropriate to the information it may collect, contain, or transmit.
- Designed to protect the device and any information it contains from unauthorized access, destruction, use, modification, or disclosure.
What does a “reasonable security feature” mean? If a connected device is equipped with a means for authentication outside a LAN it must be deemed a reasonable security feature if:
- The pre-programmed password is unique to each device manufactured.
- The device contains a security feature that requires a user to generate a new means of authentication before access is granted to the device for the first time.
The new bill follows California’s tough online privacy protection measure -- the Consumer Privacy Act approved last June -- that gives the state’s 40 million residents the right to require a business disclose the types of personal information it collects on the consumer, where that information is collected and whether it’s being sold or shared, and to opt out of the whole thing. The Act is slated to come into effect on January 1, 2020 after which companies could be docked up to $7,500 for each violation.
Will eliminating default passwords measurably improve IoT device security? It’s a step in the right direction but not a complete answer, Joe Lea, vice president of product at Armis, told Threatpost.
“Bad default passwords are problematic on multiple levels, so moving away from default passwords is a wise choice, but password hygiene won’t prevent other types of attacks targeting the tsunami of devices in the enterprise and the exposures they create,” Lea said. “There are other ways to attack these devices and exploit them. We need to recognize the extent to which these devices represent entryways onto enterprise networks and critical information.”
With the new legislation, California is ahead of the feds. A federal security standard for IoT devices for consumers would be nice. A year ago, lawmakers introduced the Internet of Things Cybersecurity Improvement Act of 2017 requiring that provide internet-connected equipment to the feds to meet various industry security standards. The Act also bars vendors from supplying IoT devices that have unchangeable passwords or known security vulnerabilities. But it's not for consumers, we'll have to wait some more.