Threat intelligence has long posed a challenge for in-house security teams and managed security service providers (MSSPs), despite the widespread adoption of threat intelligence throughout the cybersecurity industry, according to a recent study from the CyberRisk Alliance (CRA) Business Intelligence unit.
Any threat-intelligence program that uses robust, reliable data sources should reduce incident-response times and help prevent existing and emerging threats from penetrating networks and databases. But without proper mechanisms to manage the volume and velocity of threat feeds, MSSPs and in-house security teams may be easily overwhelmed, and their operations stymied by an inability to make sense of a firehose of feed data and false positives.
CRA conducted two online surveys on threat intelligence, querying IT, security and compliance professionals. The first survey, in June 2022, had 183 respondents; the second, in October 2022, had 208 respondents. Some of the respondents in the June survey were also in the October one.
"Threat intelligence enables us to make faster, more informed, data-backed security decisions and change our behavior from reactive to proactive in the fight against threat actors," said one respondent.
The June survey found that for most respondents (62%), a fear of ransomware attacks stood as the top strategic driver of their threat-intelligence strategies. This was followed by regulatory requirements (48%) and recommendations from industry experts (39%).
Other leading takeaways from the two studies included:
— The vast majority of respondents (91%) from the October survey said they used threat intelligence at some level. A large majority of respondents (70%) said security operations had become among their top use cases for threat intelligence. Most (64%) also said they used threat intelligence to increase the utility of the vulnerability-management process. Other top uses for threat intelligence included incident response (53%) and risk analysis (53%).
"Without threat intelligence you would be chasing ghosts," said one respondent to the June survey.
— Security practitioners primarily use threat intelligence to predict future attacks. A large majority of respondents (70%) from the October survey said they used threat intelligence data for operational purposes, which helps in predicting future attacks and planning defense strategies. About two-thirds (67%) said they used threat intelligence data for technical objectives, primarily focusing on attackers' resources and tools and the specific implementations used for the attacks.
— Threat intelligence has become central to security practice. Many respondents from the June survey said access to early and credible intelligence had become a core requirement. Nearly 6 in 10 (57%) said their organizations subscribed to as many as 10 threat intelligence feeds, while another quarter (26%) gathered their intelligence from between 11 and 50 feeds. The largest shares of respondents said they used threat data from malware analyses (75%) or indicators of compromise (IoCs) (72%).
— Data from existing network infrastructure are leveraged for threat intelligence. The security pros said in the October survey that the most common types of data they used for threat intelligence were from IDS, firewalls, and endpoints (reported by 67%); network traffic analysis packs and flow (62%); incident response and live forensics (57%); application logs (56%); and email or spreadsheets (55%). Use of information from the dark web (39%), MSSPs (36%), industry groups such as CERT (34%), and media/news sources (33%) were slightly less common.
— Security practitioners want to automate threat intelligence. In the June survey, respondents cited the importance of having an automated action and response capability as part of their chosen solution. Nearly half (46%) said they already incorporated automation in their threat-intelligence strategies. Almost as many (41%) said they planned to add that capability, making this the top planned component of their threat-intelligence strategies.
Overall, about 66% of respondents from the June survey said they anticipated more spending on threat intelligence in 2023. This echoes a report from the Emergen research firm that predicts the global threat-intelligence industry will double in size to $20 billion in the next five to eight years.
This bodes well for security operations centers (SOCs) and MSSPs hoping to boost defense capabilities through improved threat intelligence. However, security pros remain cautious about how much money management will let them spend, and finding the right tool to automate all these threat speeds remains challenging.
The Top 5 Challenges of Threat Intelligence

Participants in the June survey were asked to describe their top challenges or issues in effectively using threat intelligence. A shortage of qualified personnel was mentioned by 33% of respondents, edging out the changing threat landscape (30%) as the most frequently mentioned challenge.
"Finding the correct people and building processes to help make this effective" is a top issue, said one respondent.
Roughly equal shares of respondents cited budgeting and funding (20%), tools and integration (19%) and data and intelligence (19%) as among their top concerns.
"Budget is always a hot topic and never really gets better," said one respondent. "Trying to get the organization to be adaptable to new threats and to be prepared is always challenging."
Several respondents implied that threat-intelligence could be better tailored to specific industries and organizational sizes.
"Many of the current tools are not designed to work or integrate with these types of devices," said one respondent who worked in the industrial-control-system (ICS) sector. "The age of this equipment does not allow for integration or agent type installs, so upgrades to those systems are needed."
"Assessing the relevance of the intelligence to our type of organization," was cited as a top challenge by another respondent. "Much of it is centered on government, defense, or other large corporate targets rather than the smaller organizations. We have a different threat profile."
The Top 5 Benefits of Threat Intelligence
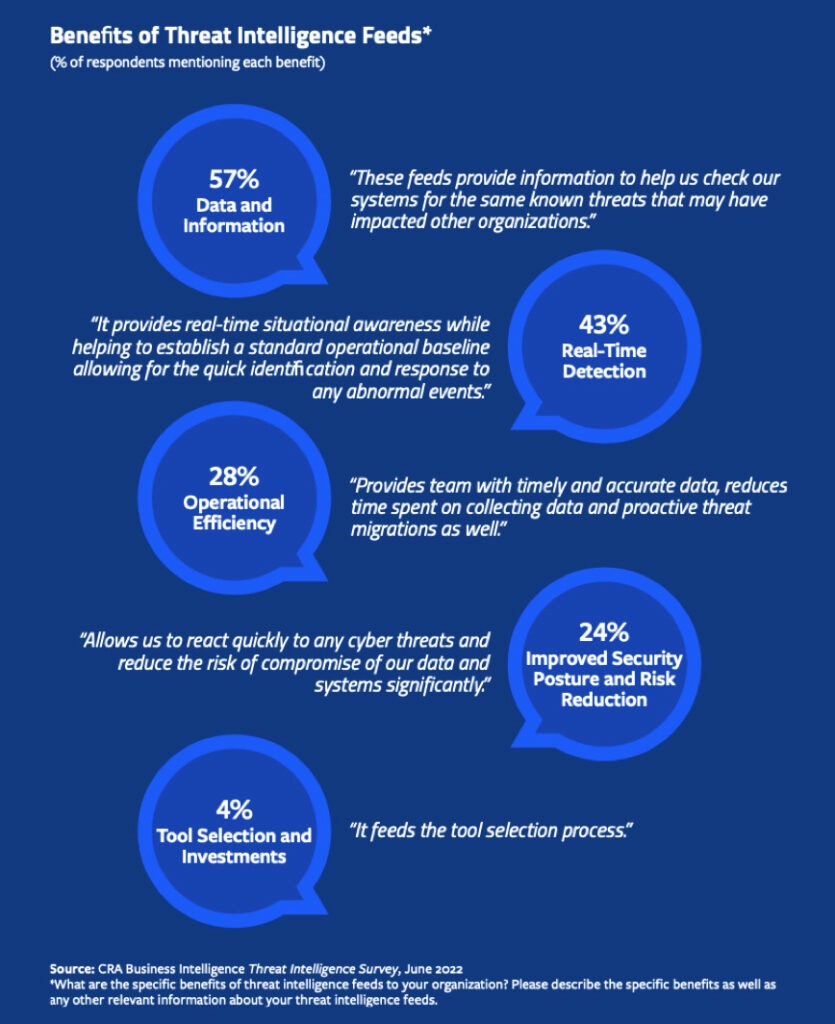
On the other hand, larger shares of respondents saw clear advantages to using threat-intelligence feeds. Fifty-seven percent of respondents in the June survey cited data and information as among the benefits of threat intelligence, while 43% mentioned real-time detection.
"It provides real-time situational awareness while helping to establish a standard operational baseline allowing for the quick identification and response to any abnormal events," said a respondent.
Operational efficiency and improved security and risk reduction were mentioned by 28% and 24% of respondents, respectively. One respondent stated that threat intelligence "allows us to react quickly to any cyber threats and reduce the risk of compromise of our data and systems significantly."
At the bottom of the list was tool selection, mentioned by only 4% of respondents.
Steve Zurier and Bill Brenner are co-authors of this article.




