The ever-evolving cyber threat landscape gives birth to new, unprecedented cyberattacks that challenge traditional cybersecurity approaches and force security operations centers (SOCs) to evolve and redefine their methods. To ensure that the integrity of their data is well-protected, SOCs have to be one step ahead of malicious actors. Ergo, the necessity of creating the modern SOC comes into play.
In this blog we’ll map out the road to creating the modern SOC, pinpoint the exact areas traditional SOCs should focus on improving, and reveal the role Sumo Logic Cloud SIEM and Cloud SOAR play in building a proactive SOC team.
Automation is the cornerstone of the modern SOC
One of the most crucial factors that dictate the success rate of SOC operations is timing. Traditional SOCs fail to assess alerts promptly and lengthy incident response times impede the ability of the SOC to prevent cyber attacks. To put things into perspective, companies need around 212 days to detect a data breach. And during that time frame, the attacker will have already achieved the intended mission, often causing irreparable damages.
Bearing this in mind, the cornerstone of state-of-the-art cybersecurity solutions, such as SOAR (Security Orchestration, Automation, and Response), revolves around the aspect of accelerating the threat hunting capabilities of the SOC. SOC teams need to be faster, more agile, and more efficient in threat hunting and incident remediation; thus, the need for introducing automation in SecOps becomes more emphasized. So, the first step in building the modern SOC starts with realizing that automation is a necessity, not a luxury, in modern security operations.
Implementing automation in SecOps, even in low-risk assignments, such as determining the IP geo-location of a domain or taking a phishing domain screenshot of incoming phishing alerts, can drastically improve the effectiveness and productivity of analysts. Even if automation saves a couple of minutes per alert, that will still result in countless hours saved, considering that most organizations get bombarded with thousands of alerts per day. In general, this is how automation helps validate building out a modern SOC:
- Faster incident response time
- More time for analysts to focus on human-scale problems
- Optimized investigation processes
- Increased capacity to make insightful decisions
- Automated reporting capabilities
- Lowered costs through reduction of manual operations
Automation gives SOC teams the edge they need to proactively enhance their threat hunting capabilities.
Progressive automation & Supervised Active Intelligence for proactive threat hunting
The foundation of the modern SOC revolves around automation—progressive automation, to be more precise. The idea is to use automation as a way to ingest and quickly analyze large quantities of data by relying on machine learning and automating all time-consuming processes that slow SOC performance.
As we mentioned before, the evolution of the threat landscape has given cybercriminals and bad actors new means of attacking. This renders reactive cybersecurity approaches obsolete and calls for a new, proactive manner of threat hunting. And, the transition from reactive to proactive threat hunting rests upon Cloud SOAR’s two distinctive capabilities:
- Progressive automation: The automation capability in Sumo Logic Cloud SOAR relies on machine learning to study the characteristics of incoming threats, recognize false positives, and provide relevant playbook recommendations to optimize response processes. In addition, you can decide whether you want to launch actions manually or automatically in playbooks. This leads to increased SecOps efficiency, improved consistency, and faster response time.
- Supervised Active Intelligence (SAI): SAI provides analysts with the information necessary to make well-informed decisions. SAI utilizes machine learning to query a user and take the knowledge extracted from incident correlation processes to help SOC teams make faster and more insightful decisions.
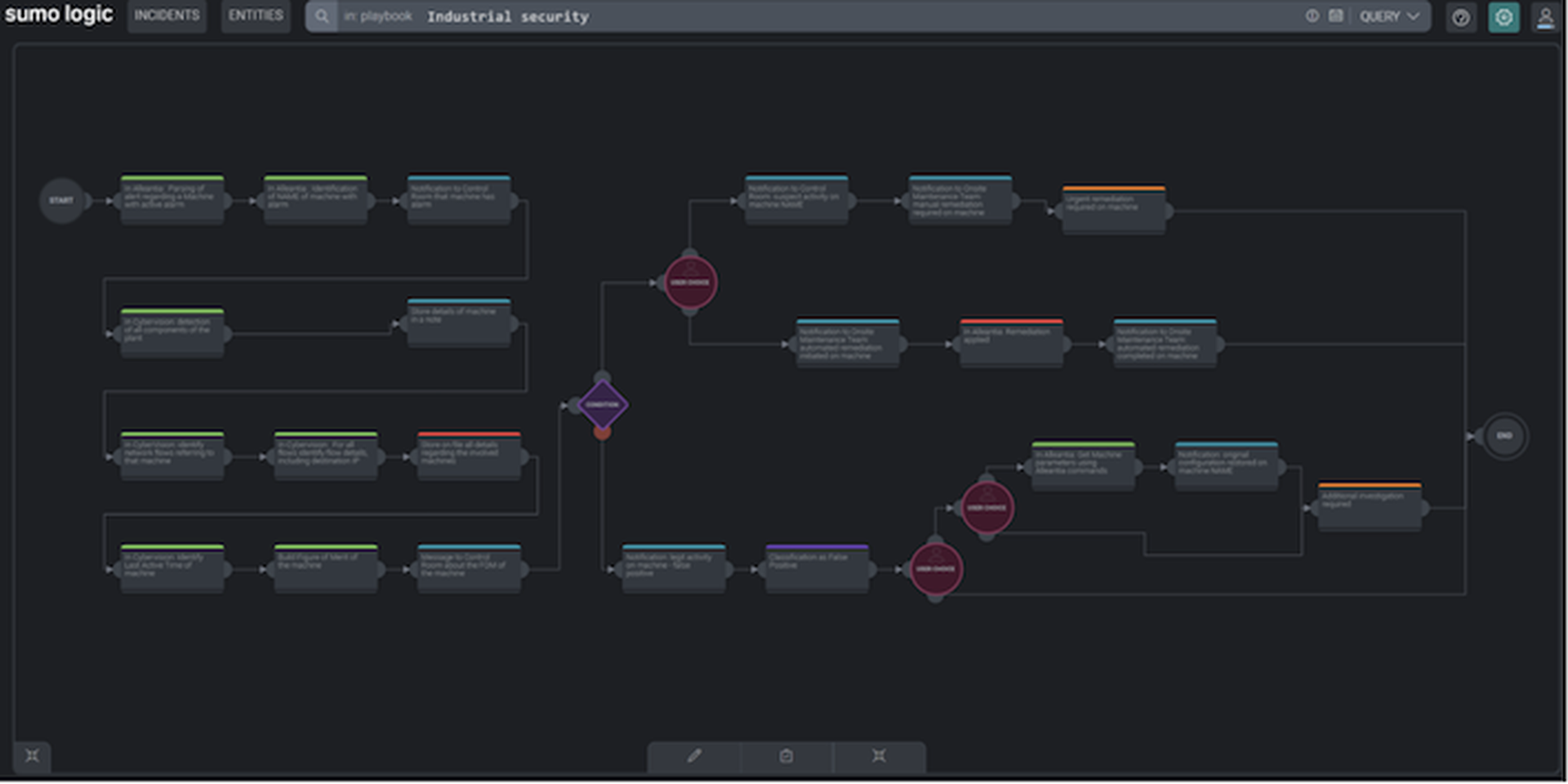
Example of playbook created as a standard operating procedure for responding to cyber incidents in an industrial environment.
In short, the basis on which both progressive automation and SAI are built is machine learning. With progressive automation, our advanced machine learning technology recommends playbooks for analysts in a “crawl/walk/run” fashion to help automate security incident response. This means decision-making and conditional responses can be made manually by human analysts, automatically by machine, or a hybrid of the two—depending on the needs, requirements, and maturity of the organization. SAI is driven by dual-mode playbooks (machine-to-human or machine-to-machine), which gives CISOs a great way to boost their SecOps thanks to machine learning without disrupting the natural workflow of their current processes.
Let’s look at how SAI and progressive automation help SOC teams in more detail:
- Eliminate false positive alerts via Triage functionality
- Empower the cyber team to activate the right processes by recommending relevant playbooks
- Improve speed, efficiency, and accuracy of SecOps
- Sharpen threat-hunting capabilities via playbooks and daemons
- Address repetitive and mundane manual tasks
- Free up more time for analysts to tackle hands-on problems
- Automatically assign tasks to the right team where human interaction is fundamental
These SAI and progressive automation capabilities revolve around improving the functionality of SOCs while still maintaining the crucial human role in SecOps. Analysts will still run the show; only now they will be augmented with the powers of automation and machine learning.
Combining Cloud SOAR & Cloud SIEM
Cloud-native SOAR and SIEM (security information and event management) tools are forward-thinking security solutions that rely on advanced capabilities to boost the performance of traditional SOCs.
With the amount of data waiting to be ingested by SOCs growing by the day, traditional SOCs can’t rely on manual labor to get the job done efficiently. This is why security solutions such as SIEM and SOAR have blossomed in the cybersecurity industry in the past decade. Even though they play two very different roles at the heart of a modern SOC, they are still intrinsically connected:
- SIEM: SIEM speeds up incident investigation processes by consolidating large amounts of data from a wide variety of sources in real-time.
- SOAR: SOAR uses machine learning to optimize and prioritize incident response activities by orchestrating multiple security tools.

SOC teams can view the latest, automatically correlated Insights in Sumo Logic Cloud SIEM
Both SIEM and SOAR connect disparate tools and use the aggregated data to provide insightful information to the security team, thus significantly easing their job in incident detection, investigation and remediation. However, both technologies have different strengths. SIEM is great at aggregating mammoth quantities of data in real-time to help analysts make data-driven decisions, while SOAR takes over after detection and makes the most of automation, orchestrating several tools in standard operating procedures (SOPs).
But the best thing about these technologies is that they don’t contradict one another. They complement each other and work together to kickstart the genesis of the modern SOC.
Cloud SOAR relies on its Open Integration Framework to easily blend within the deployed environment and integrate with different security technologies seamlessly, including Cloud SIEM. This allows analysts to maintain their existing, conventional workflow processes and utilize Cloud SOAR and Cloud SIEM harmoniously. The benefits of a Cloud SIEM and Cloud SOAR include:
- Real-time automated Insights enriched with user context
- Enhanced threat hunting capabilities
- Automated and customizable KPI reports and dashboards
- Improved visibility across multiple endpoints
- Ease of integration with hundreds of security technologies
- Faster and more efficient incident response
- Automatically-assigned manual tasks to designated analysts
- More accurate data-driven decision making by recommending relevant playbooks
- Dramatic reduction of manual and time-consuming tasks
Overall, Cloud SOAR and Cloud SIEM help SOCs get to the next level, faster. But, to achieve greater levels of proficiency in SecOps activities, SOCs will need to boost their human resources as well.
Infusing a proactive human mindset to reach the modern SOC
Keeping up the pace with evolved cyber threats requires more than just optimizing your threat intelligence portfolio. Your SOC will also need to optimize its human resources. That means changing the reactive mindset often adopted by analysts and infusing a proactive approach toward incident investigation and resolution:
- Invest in providing dedicated user training with realistic simulations using SOAR
- Teach analysts how to make the best out of forward-thinking technologies such as Cloud SOAR and Cloud SIEM
- Learn how to leverage automation to enable CISOs to make quick and insightful decisions
- Elevate the cybersecurity awareness across the perimeters of the entire organization
The last step is particularly crucial right now, as the pandemic has forced people to shift to remote working, thus eliminating the security of working under a singular and well-protected LAN network within the organization. This has elevated multiple risks, with cyber attackers eager to exploit the vulnerabilities posed by remote work environments. In this regard, Sumo Logic offers multiple cloud-native solutions that help organizations elevate their data security at all levels.
Regardless of the different types of technologies you invest in toward building your modern SOC, humans will be the ones behind the wheel making the big calls. So, it’s equally important to invest in elevating the analysts’ mindset—helping them to make the most of automation—as it is to invest in advanced security solutions. Only then you can truly be on the path to creating your modern SOC.
Learn more about becoming a Sumo Logic Partner.
Guest blog written by Enrico Benzoni & Dana Torgersen of Sumo Logic. Read more Sumo Logic guest blogs here. Regularly contributed guest blogs are part of MSSP Alert’s sponsorship program.




